NIS2 Requirements Checklist: What Your Organisation Needs in 2026

A comprehensive checklist of NIS2 Directive requirements for essential and important entities across the EU. Covers risk management, incident reporting, supply chain security, and enforcement.
The NIS2 Directive (EU 2022/2555) is the EU’s updated cybersecurity framework for essential and important entities. It replaces the original NIS Directive and introduces stricter requirements for cybersecurity governance, risk management, incident reporting, supply chain security and business continuity.
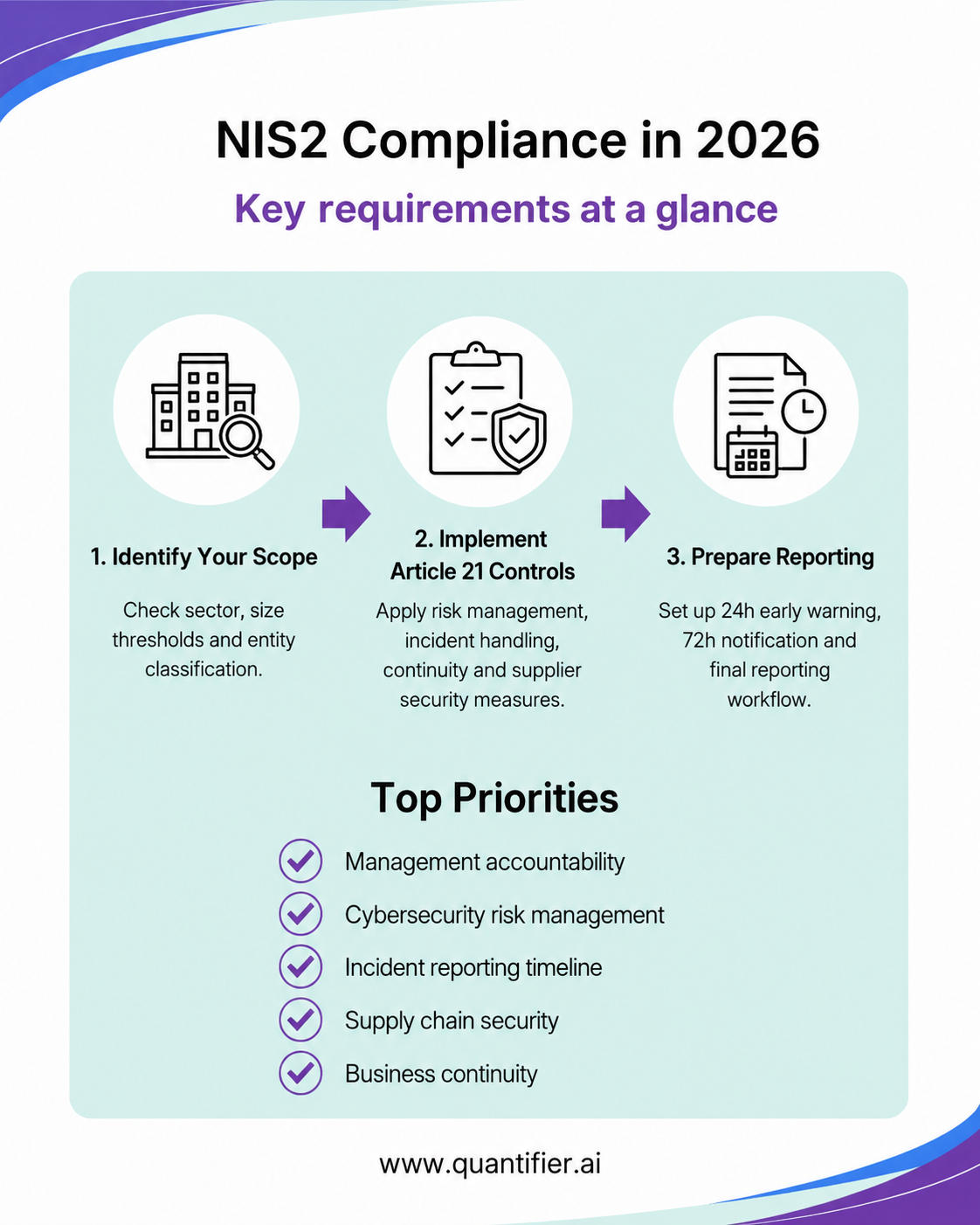
This checklist summarises the core NIS2 requirements organisations should address when preparing for compliance in 2026.
Who Needs to Comply with NIS2?
NIS2 applies to organisations operating in 18 critical and important sectors across the EU, including energy, transport, banking, healthcare, drinking water, wastewater, digital infrastructure, ICT service management, public administration, space, postal services, waste management, chemicals, food, manufacturing of critical products, digital providers and research.
The directive distinguishes between two main categories:
Essential entities: generally large organisations in high-criticality sectors, as well as certain critical providers that may be covered regardless of size.
Important entities: other medium-sized and large organisations in sectors covered by NIS2 that do not qualify as essential entities.
As a general rule, NIS2 applies to medium-sized and large organisations, typically those with at least 50 employees or annual turnover and/or balance sheet totals above EUR 10 million. However, exceptions apply, and each EU Member State implements NIS2 through national law.
NIS2 Compliance Checklist
1. Confirm Your Classification
Start by identifying whether your organisation operates in a NIS2 sector and whether it qualifies as an essential or important entity.
You should check:
- Sector and services provided
- Company size and financial thresholds
- Whether any size exemptions apply
- National implementation rules in each relevant EU country
- Registration obligations with national authorities
2. Assign Management Accountability
Under Article 20 of NIS2, management bodies are responsible for approving and overseeing cybersecurity risk management measures.
Boards and senior executives should:
- Approve cybersecurity policies and risk measures
- Oversee implementation
- Receive cybersecurity training
- Review risk and compliance reports
- Document decisions and approvals
Cybersecurity should be treated as a governance issue, not just an IT task.
3. Implement Article 21 Risk Management Measures
Article 21 requires organisations to implement appropriate and proportionate cybersecurity risk management measures.
These include:
- Risk analysis and information security policies
- Incident handling procedures
- Business continuity and disaster recovery
- Backup management
- Supply chain security
- Security in system acquisition, development and maintenance
- Vulnerability handling and disclosure
- Cyber hygiene and cybersecurity training
- Cryptography and encryption policies
- Human resources security
- Access control and asset management
- Multi-factor authentication and secure communications where appropriate
Organisations should be able to show that these measures are implemented, tested and reviewed.
4. Set Up Incident Reporting Procedures
NIS2 introduces strict reporting deadlines for significant incidents:
- Within 24 hours: early warning
- Within 72 hours: incident notification with an initial assessment
- Within one month after the incident notification: final report
Intermediate or progress reports may also be required by competent authorities or CSIRTs.
A significant incident is one that causes, or is capable of causing, serious operational disruption, financial loss or material or non-material damage to other persons or organisations.
5. Manage Supply Chain Security
NIS2 requires organisations to manage cybersecurity risks linked to suppliers and service providers.
Practical steps include:
- Identifying critical suppliers
- Assessing supplier cybersecurity posture
- Adding cybersecurity clauses to contracts
- Defining supplier incident notification duties
- Monitoring supplier security over time
- Reviewing access rights and dependencies
- Keeping supplier due diligence evidence
Supply chain security should be part of procurement, vendor management and risk management processes.
6. Prepare Business Continuity and Disaster Recovery
Organisations must be prepared to continue or restore services during and after cyber incidents.
Key actions include:
- Maintaining tested backup procedures
- Defining recovery time objectives and recovery point objectives
- Creating disaster recovery plans
- Establishing crisis management procedures
- Testing and updating continuity plans regularly
- Documenting test results and remediation actions
7. Maintain Evidence and Documentation
NIS2 compliance depends on evidence. Policies alone are not enough.
Organisations should maintain:
- Risk assessments
- Security policies and procedures
- Incident response records
- Supplier assessments
- Asset inventories
- Access reviews
- Vulnerability management records
- Training records
- Backup and disaster recovery test results
- Board approvals
- Audit evidence
A central evidence repository can make supervision, audits and internal reviews much easier.
8. Register With National Authorities Where Required
Certain entities may need to register with the relevant national authority. This may include DNS providers, TLD registries, cloud providers, data centre providers, CDN providers, managed service providers, managed security service providers, online marketplaces, search engines and social networking platforms.
Registration procedures, deadlines and required information vary by Member State.
NIS2 Penalties and Enforcement
NIS2 gives national authorities stronger supervision and enforcement powers.
Essential entities may be subject to proactive supervision, including audits, inspections and evidence requests. Important entities are generally subject to reactive supervision when there is evidence of non-compliance.
Administrative fines may reach:
- Essential entities: up to EUR 10 million or 2% of total worldwide annual turnover, whichever is higher
- Important entities: up to EUR 7 million or 1.4% of total worldwide annual turnover, whichever is higher
National laws may also define additional enforcement measures and procedures.
National Implementation Varies
NIS2 is a directive, so each EU Member State implements it through national law. This means scope, registration deadlines, reporting channels, competent authorities and transitional periods may vary.
Organisations operating in multiple countries should check local NIS2 implementation rules in each jurisdiction, including Poland, Germany, the Czech Republic and any other relevant EU markets.
Certain digital and ICT-related entities should also review Commission Implementing Regulation (EU) 2024/2690, which further specifies cybersecurity risk management measures and significant incident criteria for selected provider categories.
How Quantifier Helps With NIS2 Compliance
Quantifier.ai helps organisations prepare for and manage NIS2 compliance through an AI-native GRC platform.
Quantifier supports:
- Automated NIS2 gap analysis
- Article 21 control mapping
- Cybersecurity risk assessments
- Incident reporting workflows
- Supply chain risk management
- Business continuity evidence tracking
- Continuous compliance monitoring
- Audit-ready documentation
With Quantifier, organisations can replace fragmented spreadsheets and manual tracking with a structured, continuously monitored NIS2 compliance programme.
Request a demo to see how Quantifier can support your NIS2 readiness.
FAQ
Who needs to comply with NIS2?
NIS2 applies to medium-sized and large organisations in covered critical and important sectors across the EU. Some entities may be covered regardless of size, depending on their role and national implementation rules.
What are the main NIS2 requirements?
The main requirements include cybersecurity governance, risk management, incident reporting, supply chain security, business continuity, documentation and cooperation with national authorities.
What is the NIS2 incident reporting timeline?
NIS2 requires an early warning within 24 hours, an incident notification within 72 hours and a final report within one month after the incident notification.
What are the penalties for NIS2 non-compliance?
Essential entities may face fines of up to EUR 10 million or 2% of worldwide annual turnover. Important entities may face fines of up to EUR 7 million or 1.4% of worldwide annual turnover.